Key Findings
-
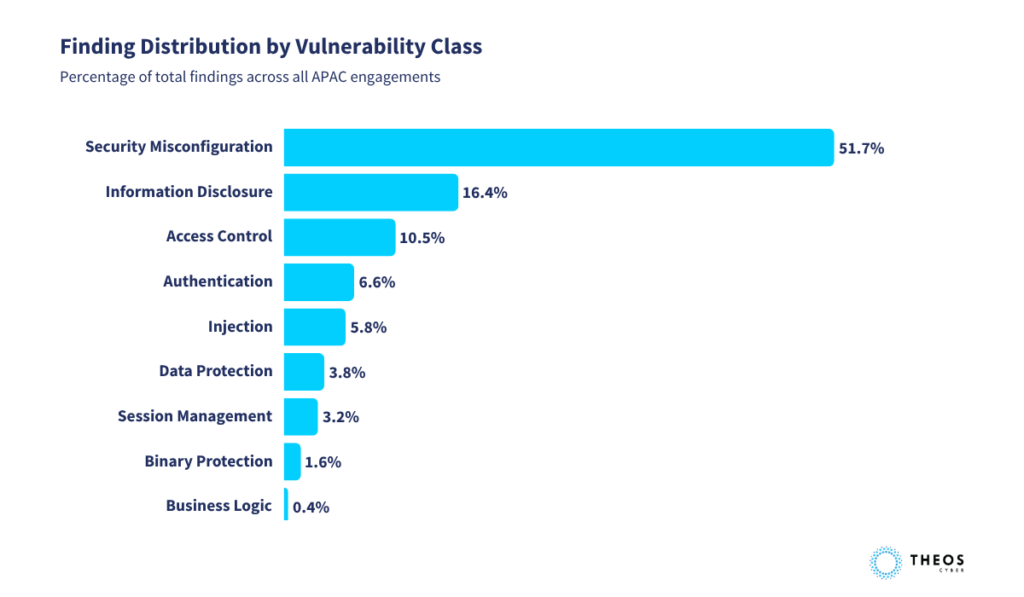
- Security misconfiguration accounts for 51.7% of all findings across APAC penetration testing engagements in 2025, making it the dominant vulnerability class by volume.
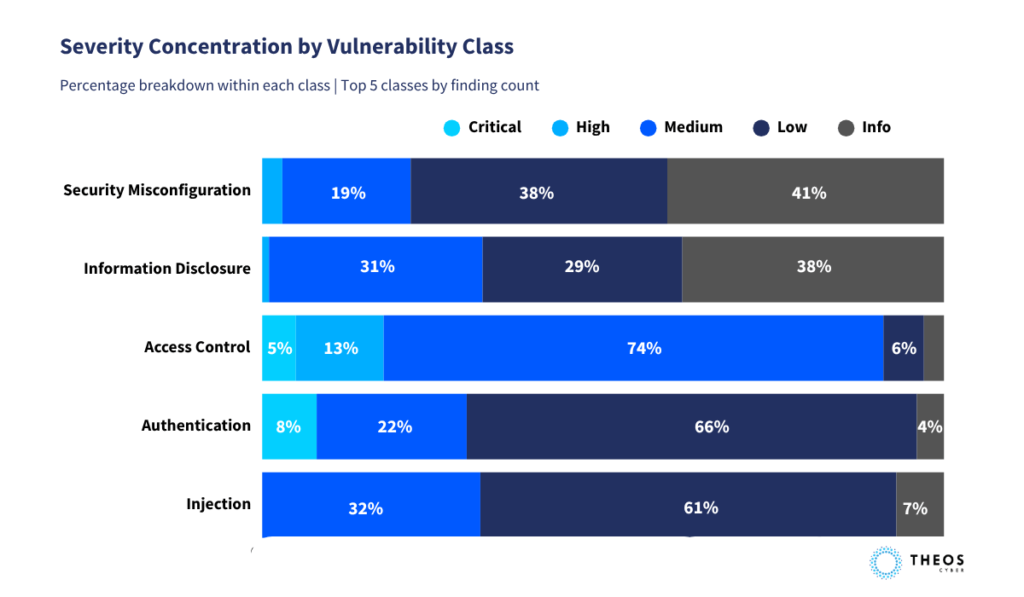
- Access control failures represent approximately 10% of total findings but carry a disproportionate concentration of high and critical severity results. Critical findings are split evenly between access control failures and authentication weaknesses.
- Injection vulnerabilities account for less than 6% of findings and produce no critical or high severity results, reflecting the risk reduction delivered by modern development frameworks.
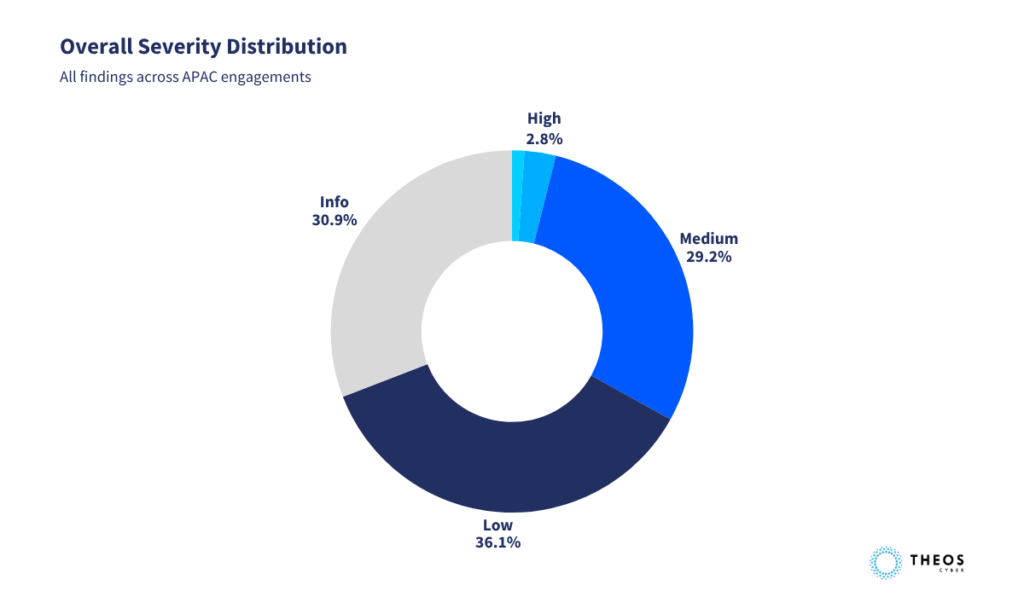
- Critical and high severity findings together represent less than 4% of the total dataset. The concentration of that 4% in access control and authentication is where the operational risk sits.
- Business logic vulnerabilities appear as a distinct finding class, representing a risk that automated scanning tools cannot surface and that compliance-driven testing programmes are likely to miss.
What does 2025 APAC penetration testing data reveal?
Security misconfiguration was the dominant vulnerability class across all engagements, accounting for 51.7% of all findings. Access control failures represented approximately 10% of total findings but carried a disproportionate concentration of high and critical severity results. Injection vulnerabilities, historically the category that drove application security priorities, accounted for less than 6% of findings and produced no critical or high–severity results.
Critical and high–severity findings together represent less than 4% of the total dataset. That distribution broadly reflects environments that have matured in foundational security practices. The number that matters operationally is where the critical and high findings concentrate. In these engagements, they concentrate in access control failures and authentication weaknesses, with critical findings split evenly between those two categories. Volume in a lower-severity class still produces material exposure. Security misconfiguration is not low risk because it is common.
Why has the APAC vulnerability landscape shifted?
Modern development frameworks have changed the code-level risk profile of enterprise applications. Parameterisation, input validation, and output encoding are handled by default in current stacks. Many of the vulnerabilities that defined application security risk a decade ago are now addressed at the framework level.
But frameworks solve coding problems. They do not solve deployment problems. The attack surface has shifted from what developers write to what administrators deploy, configure, and manage. This is visible in the evolution of the OWASP Top 10 between 2021 and 2025. Injection, has moved down as frameworks absorbed the risk. Security misconfiguration and access control failures have moved up. Cloud infrastructure is complex and configurable by nature. DevOps pipelines prioritise speed. Third-party integrations multiply the number of systems and interfaces that require correct setup and ongoing maintenance.
Security misconfiguration captures this shift precisely. It emerges when hardening is deferred under delivery pressure, when configuration baselines are assumed rather than verified, when the pace of infrastructure change outpaces the operational maturity of the teams responsible for it.
Across APAC, enterprises are running modern platforms and investing in security tooling. What the engagement data suggests is that in many environments, the governance and process layer lags behind the technology layer. The stack is current. The discipline around how that stack is configured and maintained is where the gap opens.
Why do access control failures carry the highest severity risk?
The high and critical findings in the access control category point to a specific and underappreciated weakness. The dominant pattern was access control failures at the object and function level: situations where records, transactions, or files that should be restricted to authorised users remain accessible because granular access control was not properly implemented or enforced.
This is distinct from authentication failures. An application can have functioning authentication while remaining vulnerable at the access control layer if individual resources and functions require independent validation against the requesting user’s authorisation. The surface looks protected. The exposure sits underneath.
Access control failures produce disproportionate severity for a direct reason: they represent a reliable path to unauthorised data access. They require no sophisticated exploitation technique. Standard scanning tools frequently do not detect them. They require deliberate, contextual testing that maps the application’s data model and validates access at a granular level, not just the role level.
For regulated enterprises operating under MAS TRM in Singapore, HKMA iCAST in Hong Kong, BNM RMiT in Malaysia, or the NPC framework in the Philippines, this carries direct regulatory consequences. Unauthorised access to sensitive records is a regulatory event. The path from an undetected access control failure to a breach notification obligation is short.er than most security programmes account for.
Business Logic: The invisible risk layer
Business logic flaws are not detectable through standard scanning or framework-level controls. They require a tester who understands how the application is intended to work and can probe for conditions where the logic can be manipulated: incorrect transaction flows, parameter tampering, or processes that can be exploited in ways the developers did not anticipate.
The significance of business logic findings lies in what their presence reveals: a risk class that reaches only practitioner-led contextual testing. Automated scanning and compliance-driven VAPT programmes are likely to miss it entirely.
What this means for security programmes across APAC
Three priorities emerge directly from the data.
Configuration management needs to be treated as a security discipline with the same rigour applied to vulnerability management. This means establishing hardening baselines for cloud infrastructure, applications, and network devices, validating those baselines continuously rather than at point-in-time intervals, and building processes that catch configuration drift before adversaries do. The engagement findings suggest that Mmany organisations have the tooling in place but lack the governance structure to enforce and verify configuration standards consistently.
Access control testing needs to reach below the role level to the object and function level. Custom implementations of access control, which are common across enterprise applications in this region, require contextual testing that maps the data model and validates whether individual resources and functions are correctly restricted. Assuming framework-level controls are sufficient without that validation is precisely the gap the data reveals.
Penetration testing scope needs to follow current risk concentration. Testing priorities and methodology more than two years old are likely weighted toward vulnerability classes whose critical exposure has since shifted. The 2025 findings are clear: configuration, access control, authentication, and business logic deserve primary attention in some cases ahead of the categories that historically dominated testing scope.
The shift is structural. The testing needs to follow.
The findings here come from real penetration testing engagements conducted across the Asia Pacific region in 2025. The pattern is consistent across scope, sector, and geography. The security risk surface has moved toward configuration, access control, and operational governance, and it has moved there for structural reasons that will persist.
Finding these gaps requires practitioners who test the application, not the checklist. The organisations that close that gap first are the ones an adversary walks past.
Theos Cyber is a CREST-certified cybersecurity firm delivering penetration testing and vulnerability assessment across the Asia Pacific region. The findings in this piece are aggregated from VAPT engagements conducted across APAC in 2025.

