Penetration testing (pen testing) is a critical component of any comprehensive security program. It simulates real-world attacks on computer networks or applications to scope out vulnerabilities that could be exploited by malicious actors. The primary goal is to evaluate the effectiveness of existing security measures and identify areas where an organization’s security posture is lacking. In this increasingly digital age, cyber attacks have become more sophisticated and frequent. Pen testing has become an essential tool for organizations to protect their assets, data, and reputation from potential security incidents.
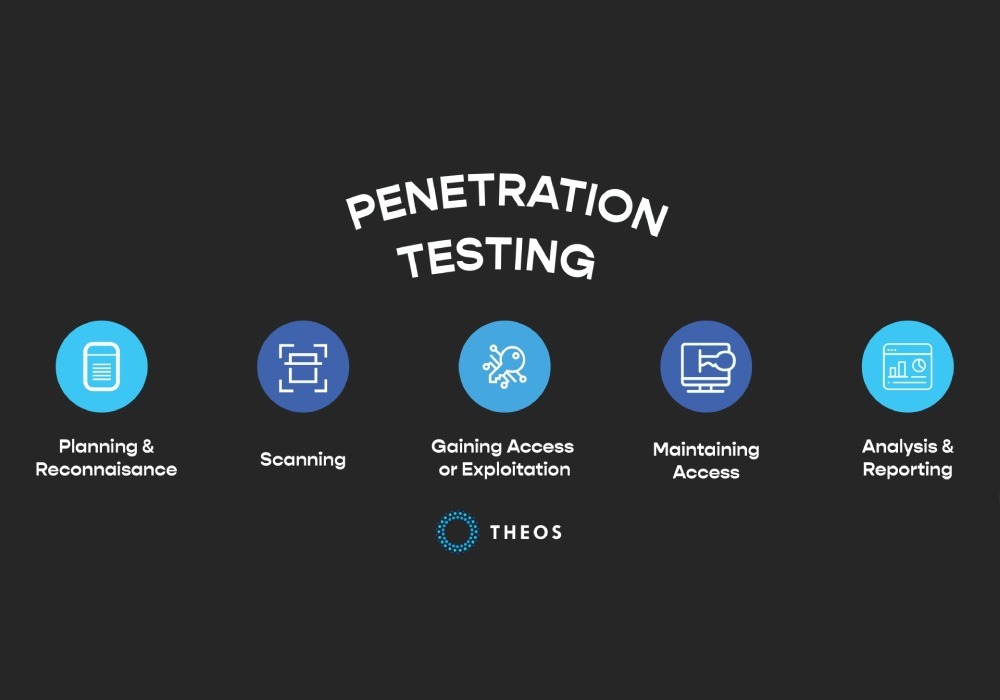
The main objective of a penetration test is to address and improve weaknesses in the security measures of a system. A penetration tester is an ethical hacker. They use a variety of techniques to try and gain access to a system, such as social engineering, network scanning, and exploitation of software vulnerabilities.
Pen Testing Methodologies
Penetration testing methodologies are techniques used to evaluate the security of computer systems, networks, or applications. There are several types of penetration testing methodologies, including black-box testing, white-box testing, and gray-box testing.
- Black-Box Testing: This method involves simulating an attack on a system without any prior knowledge of its infrastructure or security measures. The tester will attempt to find vulnerabilities and exploit them, simulating a real-world attack. This method can help identify how an attacker would gain access to a system without any insider knowledge.
- White-Box Testing: In this method, the penetration tester has complete knowledge of the system or network being tested. This can include access to source code, network diagrams, and other documentation. The tester will use this knowledge to identify vulnerabilities and exploit them. This method can help identify specific vulnerabilities in the system or network, such as configuration issues or coding errors.
- Gray-Box Testing: This method is a combination of both black-box and white-box testing. The penetration tester will have limited knowledge of the system or network being tested, such as access to a particular application. The tester will use this limited knowledge to attack and attempt to gain access to the system or network. This method can help identify vulnerabilities that may be missed in either black-box or white-box testing alone.
The choice of penetration testing methodology will depend on the specific needs of the organization. The scope of the test, the objectives, and the time and budget available will need to be considered when selecting the appropriate methodology.
Example industries that would benefit from Penetration Testing
Finance and Banking
The financial industry deals with information such as personal identification details and financial transactions making it a prime target for cyberattacks. Penetration testing can help financial institutions identify vulnerabilities in their systems and applications and ensure that their customers’ data is secure.
Healthcare
The healthcare industry handles confidential information, including medical records and personal health information. With the increasing use of electronic health records, the risk of data breaches and cyberattacks has also risen. Penetration testing can help healthcare organizations identify and mitigate vulnerabilities in their systems, ensuring that patient data is protected.
E-commerce
E-commerce companies handle vast amounts of sensitive customer data, including credit card information and personal details. Penetration testing can help e-commerce companies identify vulnerabilities in their websites and applications, ensuring that customer data is protected and transactions are secure.
In conclusion, penetration methodology testing is a vital tool in assessing the security of computer systems, networks, and web applications. By simulating attacks and identifying vulnerabilities, organizations can take proactive steps to improve their security posture and prevent potential security incidents.
Unique Data Risks by Industry
Different industries face unique data risks based on the nature of their business. Here are five examples:
- Healthcare: The healthcare industry faces unique risks due to the sensitive nature of patient data. HIPAA regulations require healthcare organizations to protect patient data and report data breaches. Cyber attacks on healthcare organizations can lead to compromised patient data and loss of trust from patients.
- Retail: Retail organizations face data risks related to credit card fraud and data breaches. Retailers collect and store large amounts of customer data, including credit card information. If this data is compromised, it can lead to financial loss for the organization and damage to its reputation.
- Financial Services: Financial institutions are a prime target for cyber attacks due to the sensitive financial data they hold. Cyber attacks on financial institutions can lead to financial loss, regulatory penalties, and damage to the institution’s reputation.
- Energy: The energy sector faces unique risks due to the critical infrastructure it operates. Cyber attacks on the energy sector can disrupt the flow of energy and cause widespread outages. This can have serious economic and social consequences.
- Education: The education sector faces unique data risks related to the large amounts of student data it collects and stores. Cyber attacks on education institutions can compromise student data, leading to identity theft and fraud.
In conclusion, a maturity assessment is an important tool for organizations to identify areas for improvement in their security posture. The assessment can help organizations prioritize security initiatives, meet compliance requirements, and improve stakeholder confidence. Failing to conduct an assessment can lead to increased risk of cyber attacks, increased cost, and non-compliance.

